It doesn't mean the «energy efficiency» rating is wrongfully stated, the statement is true, regarding electrical efficiency of the device, yet the cold produced by the device is not delivered to your house as you might think. It is split unevenly between your house and the Earth's atmosphere, where less than 1/2 is delivered to you, all the rest surprisingly enough is dumped into the atmosphere, no matter how many «pluses» they print on the energy efficiency label.
Forget about «A++++» — let's do some elementary physics

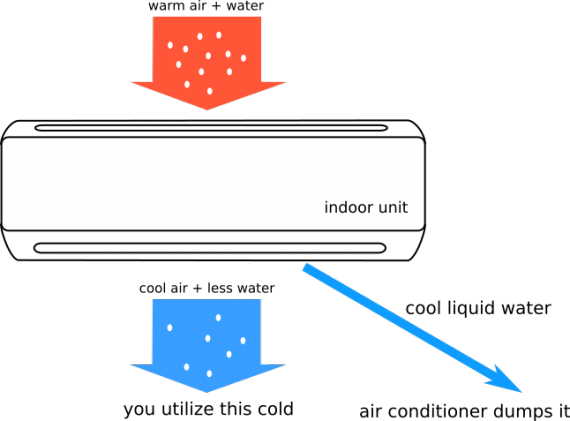
This beautiful picture is not true. Well, technically it is not entirely untrue, in absolutely dry air this picture is true, for example in Atacama desert or on Mars, but chances are the atmosphere of your house contains plenty of water, which is not mentioned on the picture. When your air conditioner cools air down it cools ALL components, of which the significant part is water vapour. The water vapour concentration is limited by the air temperature, lower the temperature lower is the maximum possible water content. That creates the
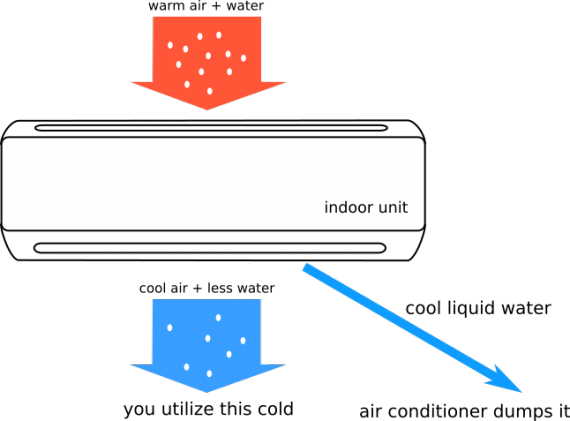
dew point phenomenon. If you drop the air temperature below a certain level water condenses out, and your air conditioner heat exchanger operates most certainly below the dew point, this is why water comes out from the device. ...And goes straight outdoors carrying the cold produced on your expense to the earth atmosphere. So that the correct scheme should look like this:
Please, stop chanting «A+++++»
Even if we assume 100% efficiency of the device,
it simply DISPOSES OF a significant part of its END PRODUCT. Now, let's us estimate how much significant is it.
Let's assume you want to cool a room down to comfortable 24 C, in a hot day (37 c, with 68% humidity, which is a typical July day in my home town).
Thus the air initially contains 0.03 kg of water per m^3.
If we now generously assume that the air pump operates at 11 C then we only need to cool 1/2 of the room volume in order to reach 24 C. It means that the heat exchanger produces 100% humid air at 11 C, which contains 0.01 kg of water per m^3.
Thus, the heat exchanger dumps 0.02 kg of cool water per m^3 of air.
Vaporization heat of water is 2257 kJ/kg, therefore your air conditioner dumps 0.02*2257 = 45.14 kJ/m^3
Let's see how big is this number.
Specific Heat capacity of humid air in our context is about 1.034 kJ/kg/K (with insignificant variation for such a rough calculation) and the density is about 1.2 kg/m^3. Thus the «consumer value» (pardon my language) of the air conditioning is roughly: 1.034*(37-24)*1.2 = 16.13 kJ/m^3
While the actually produced work consists of cooling half of the given amount of air from 37 to 11 C plus condensing water, which amounts to: (1.034*(37-11)*1.2 + 45.14)/2 = 38.7 kJ/m^3
Finally the ratio is: 16.13 / 38.7 =
0.42 — i.e. roughly 58% of the cold produced by your air conditioner goes straight outdoors.
Of course, it is a very rough estimation, but it gives you the order of magnitude of the phenomenon. Although I tried to give a conservative estimation, feel free to directly measure your air conditioner water output in order to get the precise number — I bet it will be even worse than «60%» stated in the title.
This loss does only seem inevitable!
The sad part is that this energy is completely recyclable for no cost — all you need to do is to vaporize this water on the heat exchanger of the condenser unit — BUT NOBODY CARES.