It all started as a Facebook discussion. A colleague of mine witnessed an impressive talk on a conference: a representative of a penetration testing company claimed he would hack any company in one hour. He was challenged to do this, and here is the solution:
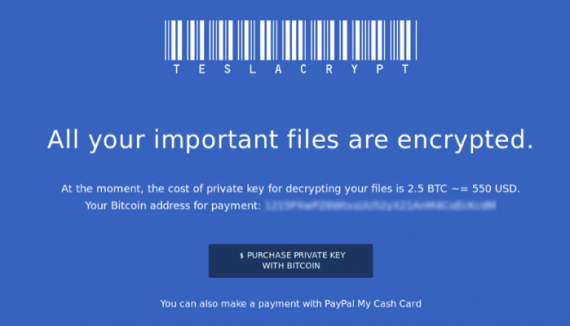
With simple search of social networks and the company’s website, he profiled the target company and obtained a contact of a sales person. Then he crafted simple trojan executable (not really tailored at this time, just some generic one), encrypted the archive and sent it to that person; then he called by phone pretending he has an urgent business proposal and mentioned the email he have just sent.
The salesperson replied: ”I cannot open the documents, my antivirus does not allow me to". «Strange, which one?» "(some name)" «Ok, I will send you a new archive, it should work». And it did (now it was a better crafted trojan).
Yes, simple as that.
Could it be thwarted with a proper training?
Yes. And no.
You may expect some vigilance from a person who understands the risks.
But what the risks are and could a training help to understand it?
From a salesperson's perspective, chances are there is a technical issue. A salesperson estimates the probability of this as, say, 90% (we may discuss his reasoning later).
“If I manage to close the deal, circumventing the procedures that do not allow me to open these documents, I get, say, $30K bonus. If I do not, I get nothing.
10% chance is there is a malicious hacker trying to steal the data from the company. If a hacker succeeds, and I get the blame, I am to be fired and I lose, say, $50K in total consequences”.
Given our salesman has a decent experience and learned some basic probability theory, it is totally acceptable for him to ignore the danger; this would be a reasonably profitable strategy that incurs no extra cost. Add some internal competition among sales people and you easily see that he would play this lottery again and again.
That's how single-parameter optimisation works. One cannot simply turn the «money seeking zombie» mode off.
Let's talk about someone a bit higher in a corporate food chain, or even at the top of it — CEO, CFO, VP of sales, etc.
The perspective changes drastically. If the contract is secured, the company gets $1M. If a large-scale network breach occurs, sensitive data get leaked, or something similarly happens, the company loses $15M. And that persons bonus is affected accordingly.
The balance is all different now (even if we assume probabilities to be the same).
Who is our CISO (or whoever is in charge of the data security) working for? The answer is obvious.
But there are caveats, as usual.
The first caveat is that if, say,
our worst-case scenario loss is estimated to be low and the associated damage to be benign, then the doing nothing strategy of risk acceptance (as bad as it sounds) is a business justified course of action.
If you dislike this choice, you may try spend some resources to decrease the probability and the impact, don't expect the business side to be very cooperative. It is still a lot of money, but not enough to let you interfere with any revenue generating processes.
And the second caveat is more serious.
It is that all our risk estimations are produced by the business risk management process, which is an enigma for us, a black box. It either works, or we blindly assume it works because it is «someone else's problem».
It the business risk management is ad hoc, or does not exist in your organisation, or is non-functional, it gets substituted with “information security risk management”, where the most prominent «information sources» are: «FBI/CSI reports», «SEC-mandated leak disclosures», «industry analysis reports» — the highest grade nonsense, zero relevance is guaranteed.
It is better than nothing to base our guess on, but a blatant attempt to sell our qualitative estimation as quantitative data is a pure hoax.
However, chances are there is no risk management at all in your company, not even a dysfunctional one.
I think most people in the industry know that, but most are afraid to tell the truth aloud.
If you do not know your business environment, the probability estimation is pointless.
If you do not know the real business impact of a breach, your loss estimation is baseless.
Multiply these to get nonsense squared.
But you need to “justify” your security choices anyway. Scaremongering sounds like a decent plan now?