Dear mr. Thunderf00t, recently you have published a series of videos about melting gold in strange contraptions (or one might say «stupid setups»). This series culminated in the
episode called «Will Burning Diamond Melt Gold?». I quote:
Gold melts at 1064 C, Diamond burns at 2700 C — this should be enough to melt gold, will a diamond melt gold?
Then you put a ~0.25g diamond on a 1g golden coin, ignite the diamond in the pure oxygen atmosphere and wait until the diamond burns a hole in the coin. The diamond burned happily to ashes and the coin remained intact.
This «failure» created confusion among yourself and your audience:
How so?! It burnt so HOOOOOOOT! and melted nothing...
Spoiler alert: ENERGY TRANSFER.
Given that few days before you successfully melted a bead of gold that was put in a cavity inside a burning graphite block (What a surprise that this contraption worked!), your confusion is legitimately cringeworthy.
FUCKING SHAME!!!
I want you to understand the magnitude of this shame. Mr. Thunderf00t is not only an official scientist like many imbeciles are, he has a real discovery in his portfolio which is an achievement that the Steven Hawking's portfolio lacks of. Mr. Thunderf00t is a real scientist — not a cosmologist or something — he knows his science and he is capable of conducting meaningful experiments.
A man of this qualification was driven astray by the notion of temperature. So much astray, that laymen of ancient Egypt would laugh at his «gold melting» contraptions being so obviously against even the most basic common sense understanding of thermodynamics available for humans since 10 000 years ago… 20 000? Once again, pay attention, a credible scientist forgets to calculate the energy balance of his experiment before burning real diamonds.
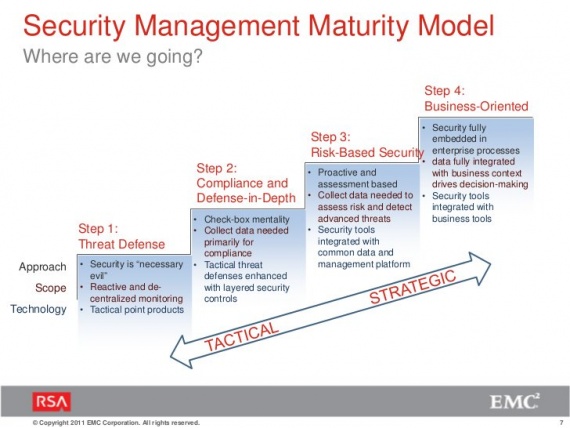
I therefore propose to remove the notion of temperature from the middle school physics curriculum, for it is overwhelmingly confusing and marginally useful.
P.S.
make a funny experiment:
calculate «the temperature» of a 10 GEv proton, say X (note the amount of zeroes in the result)
and then ask a patented physicist: will a proton heated up to X Celcius deg melt a hole in a thin golden foil.