Before you indulge into an experiment investigating the effects of whatever quality of a subject, it is the best for you to make sure beforehand that the quality in question does belong to your subject.
We colloquially say: «a red pencil» as if it is not a question whether a pencil can be red. Indeed, it can. In this particular case our «intuition» coincide with physical reality. We can create an experiment that demonstrates a possibility of any colour be a quality of a pencil. We can clearly define «red» as a specific feature of the light spectrum, and we can unambiguously link those spectra to each pencil. We can see (experimentally) that some pencils share this quality, while some do not. Even if the dividing line between these sets is fuzzy, we now have a CHARACTERISTIC PROPERTY of a «red pencil»: all red pencils share this property, and all non red do not have it. Facing a pencil, we can (experimentally) determine if it is red (and to what extent).
It is perfectly legitimate for anyone to call a pencil «red» or otherwise tag a pencil with a colour, because of the physics, not because the language allows it. Language is equally suitable for describing reality and nonsense as well. We still can call a pencil «aggressive» but it does not make physical sense. Aggressiveness can not be observed in pencils. There are many qualities applicable to pencils and there are many qualities inapplicable to pencils. Some qualities are plainly inapplicable to some objects — this fact is so basic that is often forgotten.
Now, I give you two grains of wheat, one is «GMO» and another isn't.
Can you conceive an experiment that tells me which is which?
Maybe it is time to make one step back and determine if «GMO» is a quality of an organism? Is there any CHARACTERISTIC PROPERTY of a «GM organism», something that all «GM» subjects share, while none of the rest have? Please, define this property for me. ...or simply ask yourself (every time you are looking for the magical label on the food package)
what is this characteristic property I am looking for?
Now, as you have yelled at me all your suggestions, think carefully which of them is actually a property of an organism. Not single one. All that you have come up with are qualities of a production process or a design process or even earlier. None of those can be observed in a grain of wheat.
Observing a car, can you tell, for example, a difference between a car that was sketched with HB pencil and a car sketched with 2B pencil during their stage of development? In case of a car you would not claim that all qualities of a design phase are inherited by the product. You may consider me foolish to even suggest this very possibility. It is too obvious for you that a car and a car production process are two wildly different objects. Ok, then. What makes you claim that «GM» property of an organism design process is also a quality of a resulted organism? Hopefully you are not going to claim that organisms and their production processes are the same object.
However, you may legitimately conjecture that this particular property somehow translates from the design process to the organism. This is why I gave you these two grains of wheat. Take them and prove your conjecture. Show me the CHARACTERISTIC PROPERTY of «GMO».
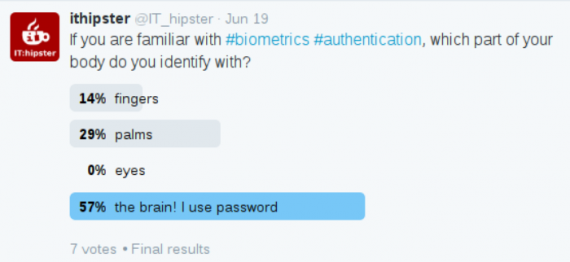
I know you are wondering what all this nonsense has to do with passwords.
Well, this is all about the information entropy, which you do happily assign to your passwords without even a glimpse of doubt:
IS IT REALLY A QUALITY OF A PASSWORD??? CAN I CREATE A CHARACTERISTIC RELATION THAT MAPS PASSWORDS ON REAL NUMBERS AND IS A FUNCTION???